Summary
| The challenge | Finding the most convenient SSO architecture for a new Data Center instance of Jira without losing the ability to sync valuable fields, like supervisor roles |
| The Atlassian Stack | – Jira Data Center 1,000 users – Confluence Data Center 1,000 users |
| Solution | Combine the native Atlassian Data Center SSO for authentication with resolution’s User Sync for user provisioning, deprovisioning, and updates |
| Benefits | – Maximum value for minimum cost of all possible scenarios – A complex approval process perfectly synced in Jira |
A hybrid migration to Data Center SAML SSO and User Sync
In a migration to Data Center, User Management processes, including authentication and user provisioning processes, need to be analyzed separately to find the most convenient solution.
Sixt Lease’s architecture is a good example of how to leverage existing functionality in Data Center applications with the most advanced apps from the Marketplace. One of their top requirements was to keep supervisor roles in sync. People come and go quite frequently, and having a tight process to ensure that the right supervisors were immediately carried over to Jira after a change in the IdP was essential.
The following timeline shows how it happened.
Sixt Leasing’s move to Jira Data Center
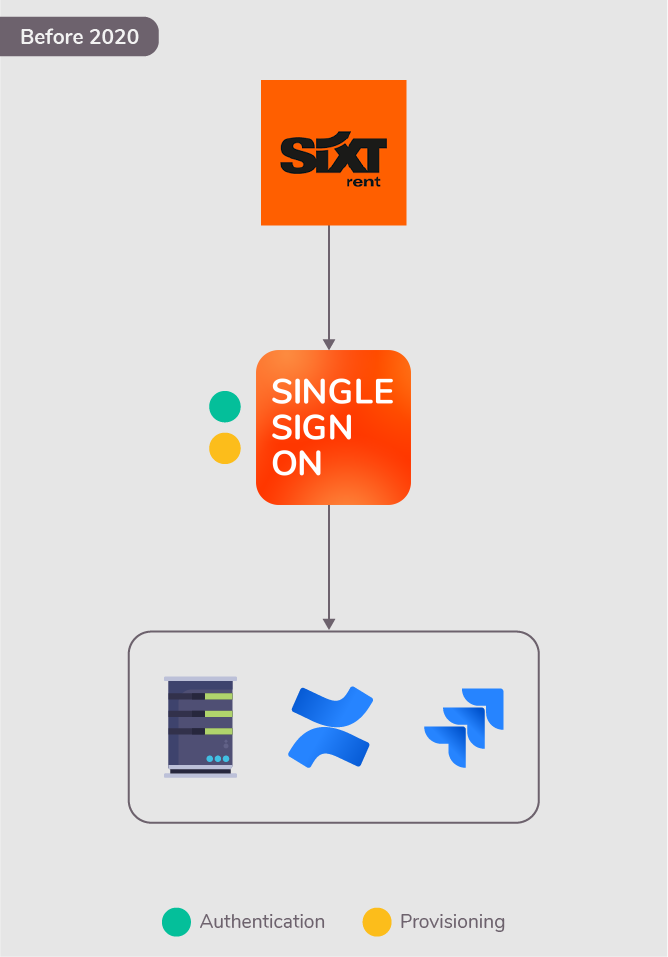
In early 2020, Sixt Leasing decided to have their own Jira and Confluence instances on Data Center, segregating from Sixt’s Server instance.
Customizations and third party add-ons were evaluated by TNG consulting and IT Management at Sixt Leasing to decide whether they would be carried over to the new instance. Two main criteria were used:
- Sufficient usage by Sixt Leasing employees and projects.
- Existence of a Data Center compatible version.
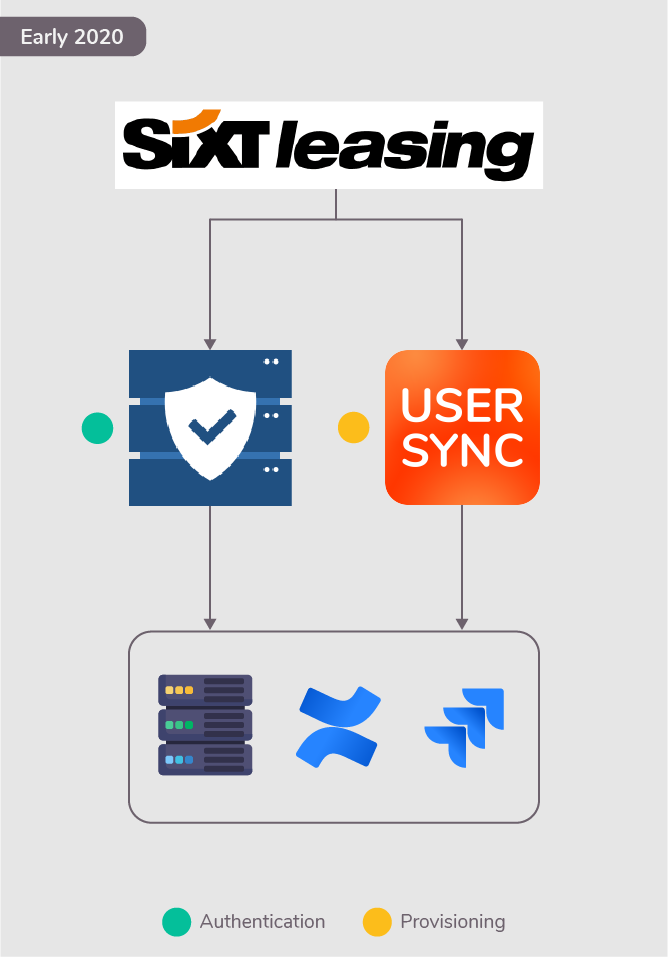
A hybrid SSO setup: SAML-based authentication and REST user provisioning
When the time arrived for resolution’s Single Sign-On, this was the verdict:
- Atlassian’s native Data Center SAML SSO could replace user authentication…
- but it could not solve user provisioning.
TNG’s consultants started looking for an add-on that could provision users seamlessly. They looked first at similar apps from their current vendor, and found an alternative quickly.
Their recommendation was User Sync, resolution’s app that integrates user directories of Atlassian applications and Identity Providers via REST API. No code needed.
Therefore, Sixt leasing implemented a solution:
- where Data Center native SAML SSO is used to authenticate users
- And User Sync is used to provision and de-provision users
Evaluating Atlassian’s Just in Time provisioning as an alternative to User Sync

In September 2020, Atlassian launched Just in Time user provisioning for its Data Center SAML SSO.
At this point, SIXT leasing reconsidered its SSO setup. They had the chance to drop User Sync and only use the built-in functionality instead.
The benefits were clear: lower costs, and a simpler implementation.
So why wasn’t User Sync dropped?
An approval process in perfect sync
A vital business logic would have been damaged, had User Sync been dropped.
Data Center Just in Time can’t update supervisor roles for a very simple reason: JiT only updates the information of a user when they successfully login. This means that supervisor roles would be outdated, and that an additional manual workstream would have to be created in Jira to manage those roles or to ensure that managers log in before approval assignments are sent by their reporters. That was a deal breaker.
With User Sync, in contrast, issue approvals are reliable at all times. Regardless of whether users with supervisor roles are faster than their reporters logging into Jira for the first time.
How Sixt Leasing runs their approvals with User Sync
Every employee at Sixt Leasing is assigned a supervisor who is responsible for approvals. The approval process is based on a scriptRunner workflow validation. Only the supervisor and the supervisor’s supervisor can approve an issue, i.e. perform a specific workflow transition.
Supervisor roles are stored in the external directory as a user attribute. Since they change frequently, they are only maintained on the Identity Provider. From there, they should propagate to several tools, including Jira.
Supervisor attributes are synchronized into Jira with User Sync.
Conclusion
IT management and TNG consultants agreed it was beneficial to stick to the initial design. User Sync provisions and updates users, and Data Center SAML SSO deals only with authentication.
As a result, Sixt Leasing can benefit from the advantages of the SSO functionality shipped with Data Center Applications, and enforce its approval processes in Jira at all times.
About Sixt Leasing

Sixt Leasing SE, a former subsidiary of Sixt SE later rebranded as Allane SE, is one of Germany’s leading vehicle leasing providers with subsidiaries in Austria, Switzerland, France and the Netherlands. Independent from manufacturers and banks, Sixt GmbH & Co. Autovermietung KG provides full-service leasing solutions for corporate customers, as well as car rents for private and commercial customers through a convenient, fully configurable and cost-efficient online platform.
About TNG Tech Consulting
TNG Technology Consulting is an Atlassian Gold Solution Partner and Atlassian Marketplace Vendor. Their model is based on value-based consulting partnership focused on high end information technology with a service offering in agile software development, Artificial Intelligence, and DevOps and Cloud.
